Cyber Case Study: SolarWinds Supply Chain Cyberattack - Ollis/Akers/Arney Insurance & Business Advisors

PDF) Cyber security in the age of COVID-19: A timeline and analysis of cyber-crime and cyber-attacks during the pandemic | Harjinder Lallie - Academia.edu

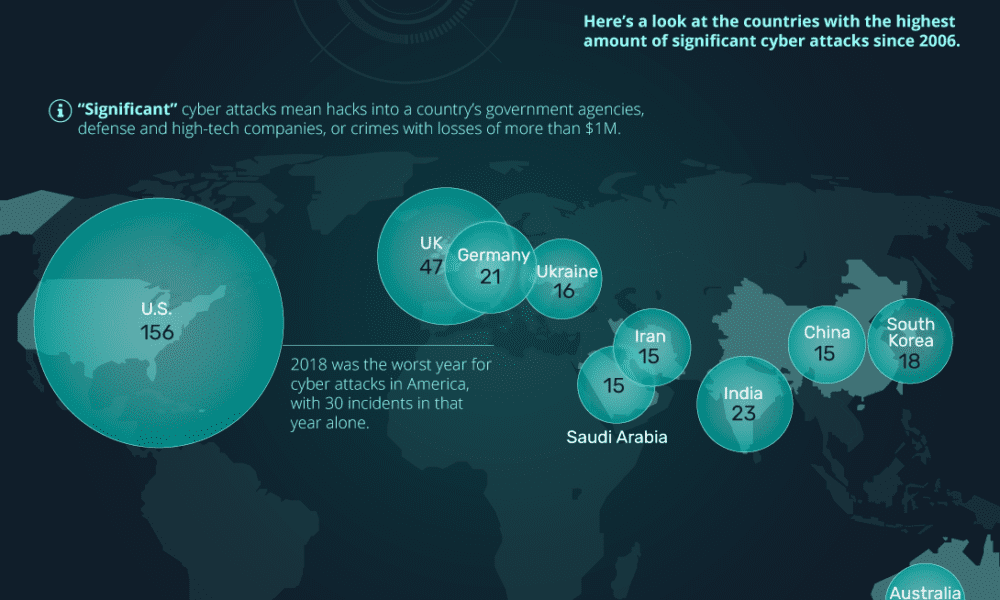
Morning brief: Over 670k cyber attack cases in India this year so far | Latest News India - Hindustan Times

A coordinated nation-state cyber attack is a worst-case scenario, says former U.S. chief technology officer

a) Human aspects of cyber threats. (b) Summary of the factors in Table 2. | Download Scientific Diagram

Cyber Attacks, Attribution, and Deterrence: Case Studies – Stuxnet Attack on Iran, LulzSec, and Estonian Attacks, Protection of Cyberspace and Digital Infrastructure as Vital to National Security eBook by Progressive Management -
Cyber Attack Case Study Ppt Powerpoint Presentation Visuals | Presentation Graphics | Presentation PowerPoint Example | Slide Templates